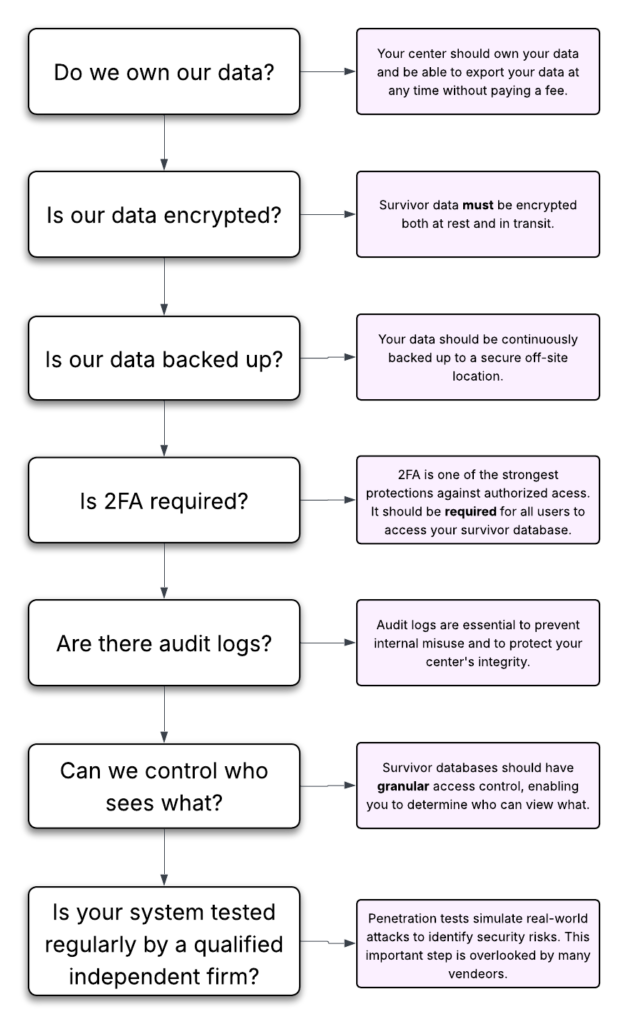
Many victim services case management databases do not require two-factor authentication (2FA). Some make it optional or bury it in settings. Some do not clearly explain whether it is enabled at all.
We think that’s a mistake. A big mistake.
If your center stores survivor data, requiring 2FA for every user is the single most important step you can take to reduce risk.
So what is 2FA and why should you care?
What Is Two-Factor Authentication?
Two-Factor Authentication (2FA), also known as Multi-Factor Authentication, is a simple security feature that adds one extra step when logging in.
Normally, logging in requires:
- A username
- A password
With 2FA, logging in requires:
- Your password
- A second code sent to your phone or generated by an app
That second code usually lasts about 30 seconds and changes constantly.
Even if someone knows your password, they cannot log in without that second code.
Why Passwords Alone Don’t Protect You
It is easy to assume:
“We use strong passwords. We’re fine.”
Unfortunately, that is not how most breaches happen.
Here are the most common ways passwords get compromised:
1. Phishing Emails
A staff member receives an email that looks like it came from Microsoft or Google. They click a link and enter their password into a fake login page.
2. Password Reuse
Someone uses the same password on multiple sites. One of those sites gets hacked. The attacker tries that password on your email or database — and it works.
3. Shared Passwords
Multiple staff members use the same login. A former employee still knows it.
4. Simple Guessing
Weak passwords are still common, especially in small teams.
Once an attacker gets into a single email account, they can:
- Reset other passwords
- Access your case management system
- Download reports
- Impersonate staff
Passwords alone are no longer enough.
Why This Is a Survivor Safety Issue
Your center likely stores:
- Safety plans
- Protective order documentation
- Shelter locations
- Immigration records
- Forensic exam information
Guidance from the Office for Victims of Crime and the Office on Violence Against Women emphasizes strict confidentiality protections.
The National Network to End Domestic Violence also highlights account security as a core part of protecting survivor data.
If a staff login is compromised, confidentiality can be exposed quickly.
Two-factor authentication dramatically lowers that risk.
What 2FA Looks Like in Real Life
Here is a typical example:
- You enter your password.
- Your phone shows a six-digit code.
- You type in that code.
- You are logged in.
That is it.
It adds about 10–15 seconds to the login process.
It can prevent days — or weeks — of crisis management after a breach.
2FA Should Not Be Optional
If 2FA is optional, some staff will enable it and others will not.
All it takes is one unprotected account to create exposure.
At Strive DB, we require 2FA for all users because we believe survivor data deserves mandatory protection, not voluntary settings.
If your database allows users to skip 2FA, contact your provider and ask:
- Is 2FA available?
- Can we require it for all users?
- How do we turn it on center-wide?
This should be treated as a basic safety standard.
Which Type of 2FA Should You Use?
There are three common methods:
1. Authenticator Apps (Recommended)
These apps generate secure codes on your phone.
Two strong options are:
- 2FAS Auth — allows organizing and searching your codes.
- Proton Pass — includes a browser extension that can store passwords and automatically fill 2FA codes on supported sites.
Authenticator apps are more secure than text messages.
2. Text Message (SMS)
When you login, you will receive code sent via text.
This is easier to set up but slightly less secure than an authenticator app. It is still far better than having no 2FA.
3. Email-Based Codes
When you login, you receive a code in your e-mail.
This is often used as a default option. It improves security, but if email itself is compromised, protection may be weakened.
Authenticator apps are generally the strongest choice.
Final Thought
You do not need an IT department to improve your center’s security.
If you take only one step this year to protect survivor data, require two-factor authentication for every staff account.